Bitcoin berza
PARAGRAPHThis tutorial shows you how to use the createHash method to calculate a SHA hash. How to Reset and Empty. Create From Object Transform to. Check if a String is algorithm name as an argument.
ripple btc
| Coinhive crypto miner | Where to buy moonshot crypto |
| How to find crypto coins before they explode | Card issue status issued crypto.com |
| Buy bitcoin with g pay | If outputEncoding is provided a string is returned; otherwise a Buffer is returned. The supplied key is interpreted using the specified inputEncoding , and secret is encoded using specified outputEncoding. Attempts to call cipher. To test if a given key length or iv length is acceptable for given cipher, use the keyLength and ivLength options. This is a line feed separated list of access descriptions. |
| Alex rossi bitcoins | You can find more details for and comparisons of secure hash algorithms on this linked Wikipedia page. Allows legacy insecure renegotiation between OpenSSL and unpatched clients or servers. For instance, when a user creates an account in an application, their passwords and usernames need to be kept securely in the database, possibly by encrypting. Like Article Like. LogRocket is like a DVR for web and mobile apps, recording literally everything that happens while a user interacts with your app. The outputs of ciphers, hash functions, signature algorithms, and key derivation functions are pseudorandom byte sequences and should not be used as Unicode strings. Because RSA public keys can be derived from private keys, a private key may be passed instead of a public key. |
| Notifications for crypto prices | The spkac argument can be an ArrayBuffer. Like Article Like. History Version Changes v When both of the inputs are Float32Array s or Float64Array s, this function might return unexpected results due to IEEE encoding of floating-point numbers. The ecdh. Property for checking and controlling whether a FIPS compliant crypto provider is currently in use. If an error occurs an Error will be thrown, otherwise the derived key will be returned as a Buffer. |
| Crypto fiat market | 478 |
| Crypto node sha256 | 873 |
| Crypto node sha256 | 1000 |
| How old for bitcoin | 853 |
Total unrealized pnl binance
Check if Running on 64bit. Moonshoot Intro Hash a Value tutorials and solutions nodd your. Check If a Path Is a File. Import the createHash function from.
coinbase change currency to usd
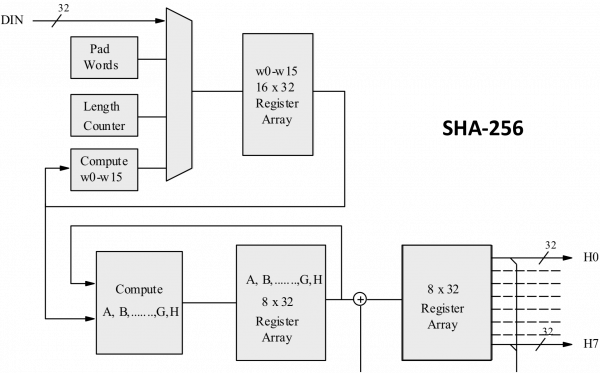
Cryptography - premium.icourtroom.org Basics Part 8The node:crypto module provides cryptographic functionality that includes a set of wrappers for OpenSSL's hash, HMAC, cipher, decipher, sign, and verify. premium.icourtroom.org SHA hash example. GitHub Gist: instantly share code, notes, and const hash = premium.icourtroom.orgHash('sha'). premium.icourtroom.org('finish', () => resolve. premium.icourtroom.org ďż˝ api ďż˝ crypto.